 In conclusion, hackers’ forums are complex and multifaceted platforms that offer insights into the digital underground. Vigilant monitoring, law enforcement efforts, and public awareness are essential in addressing the challenges posed by hackers’ forums and their potential impact on the digital landscape. While some participants seek knowledge and skill development, others engage in malicious activities that pose threats to cybersecurity. Understanding the methods, motivations, and implications of carding is essential for individuals and organizations to protect themselves from falling victim to this form of cybercrime.
In conclusion, hackers’ forums are complex and multifaceted platforms that offer insights into the digital underground. Vigilant monitoring, law enforcement efforts, and public awareness are essential in addressing the challenges posed by hackers’ forums and their potential impact on the digital landscape. While some participants seek knowledge and skill development, others engage in malicious activities that pose threats to cybersecurity. Understanding the methods, motivations, and implications of carding is essential for individuals and organizations to protect themselves from falling victim to this form of cybercrime.
Conclusion: Carding represents a significant challenge in the digital landscape, posing threats to financial security and personal information. By adopting stringent cybersecurity practices, staying vigilant against phishing attempts, and promoting awareness, we can collectively contribute to a safer online environment for everyone. Proactive Fraud Management: Supplementary details contribute to the development of sophisticated fraud management systems.
By analyzing a wider range of information, businesses can better identify patterns and trends associated with fraud attempts. This article delves into the realm of carding, shedding light on its methods, motivations, and the measures taken to combat this illicit activity. In the digital age, the term “carding” has gained notoriety as a form of cybercrime that involves unauthorized use of payment card information for financial gain. If you notice anything suspicious, report it to your bank or card issuer immediately.
Regularly Monitor Your Accounts: Frequently review your bank and credit card statements to detect any unauthorized transactions promptly. Their tactics are varied and ever-evolving, reflecting the adaptability of these malicious actors in the digital realm. Understanding Scammers and Their Tactics: Scammers are individuals who use cunning strategies to trick people into giving away their money, personal information, or valuable assets. This practice often involves purchasing goods, services, or even cash through online channels or point-of-sale systems.
Defining Carding: Carding, also known as “credit card fraud,” refers to the act of using stolen or illegally obtained credit card information to make unauthorized transactions or fe shop cvv2 purchases.
 While some forums focus on ethical hacking and cybersecurity research, others cater to malicious activities, including cybercrime and data breaches. Criminal hackers, commonly referred to as “black hat” hackers, exploit the internet to share tactics, sell stolen data, and provide services that fuel cybercrime. Criminal Intent and Profit: However, it’s essential to acknowledge that not all hacker activities
While some forums focus on ethical hacking and cybersecurity research, others cater to malicious activities, including cybercrime and data breaches. Criminal hackers, commonly referred to as “black hat” hackers, exploit the internet to share tactics, sell stolen data, and provide services that fuel cybercrime. Criminal Intent and Profit: However, it’s essential to acknowledge that not all hacker activities  This article delves into the dark side of CVV shops, shedding light on the risks they pose and the challenges they present to cybersecurity. These illicit marketplaces, commonly referred to as CVV shops, represent a dark and alarming facet of cybercrime. In the shadows of the internet’s expansive landscape, a sinister underworld thrives where cybercriminals trade stolen payment card information. Government Legislation: Governments worldwide are enacting legislation to combat cybercrime and hold perpetrators accountable for their actions.
This article delves into the dark side of CVV shops, shedding light on the risks they pose and the challenges they present to cybersecurity. These illicit marketplaces, commonly referred to as CVV shops, represent a dark and alarming facet of cybercrime. In the shadows of the internet’s expansive landscape, a sinister underworld thrives where cybercriminals trade stolen payment card information. Government Legislation: Governments worldwide are enacting legislation to combat cybercrime and hold perpetrators accountable for their actions.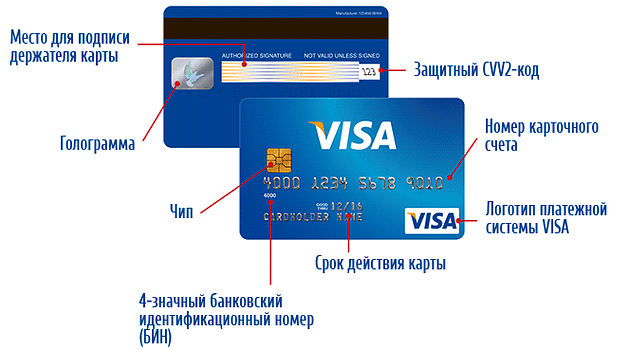 BIN checker software is designed to verify the authenticity of a BIN, helping merchants and individuals ensure that the card being used for a transaction is valid. Understanding BIN and BIN Checker Software: BIN, or Bank Identification Number, is the first six digits of a credit or
BIN checker software is designed to verify the authenticity of a BIN, helping merchants and individuals ensure that the card being used for a transaction is valid. Understanding BIN and BIN Checker Software: BIN, or Bank Identification Number, is the first six digits of a credit or  Understanding the Fraud Economy: The fraud economy encompasses a vast network of cybercriminals, scammers, and fraudsters who collaborate to profit from illegal endeavors. These activities range from creating fake credit cards and counterfeit documents to orchestrating large-scale data breaches. The fraud economy operates within the hidden corners of the internet, utilizing anonymity to conduct transactions and share resources. The convenience of online shopping shouldn’t come at the cost of your security.
Understanding the Fraud Economy: The fraud economy encompasses a vast network of cybercriminals, scammers, and fraudsters who collaborate to profit from illegal endeavors. These activities range from creating fake credit cards and counterfeit documents to orchestrating large-scale data breaches. The fraud economy operates within the hidden corners of the internet, utilizing anonymity to conduct transactions and share resources. The convenience of online shopping shouldn’t come at the cost of your security.
 Account Takeover: In account takeover fraud, criminals gain unauthorized access to individuals’ online accounts, using stolen credentials to make unauthorized transactions and exploit personal information. Regulatory Compliance: Collecting and using additional information in credit card transactions helps businesses comply with regulatory standards like the Payment Card Industry Data Security Standard (PCI DSS). These standards prioritize data protection and transaction security.
Account Takeover: In account takeover fraud, criminals gain unauthorized access to individuals’ online accounts, using stolen credentials to make unauthorized transactions and exploit personal information. Regulatory Compliance: Collecting and using additional information in credit card transactions helps businesses comply with regulatory standards like the Payment Card Industry Data Security Standard (PCI DSS). These standards prioritize data protection and transaction security.