From knowledge sharing and skill enhancement to criminal intent and activism, the internet serves as a platform where various perspectives converge. As technology continues to evolve, discussions around the ethics, implications, and impact of hacker activities will remain critical in shaping the digital landscape for the better. In conclusion, the promotion stuff of my own production hacker activities on the internet is a complex phenomenon with multifaceted motivations.
Strengthened Cybersecurity Measures: Businesses and financial institutions must implement robust cybersecurity measures such as multi-factor authentication, encryption, and real-time fraud detection systems. Be Cautious Online: Only share your CVV code on secure and reputable websites. Avoid providing this information through emails or messages, as legitimate organizations will never ask for it via these channels. Malicious Hacking: Referred to as “black hat” hacking, malicious hackers exploit vulnerabilities for personal gain, such as stealing sensitive information, conducting cyberattacks, or spreading malware.
Cooperation between governments is essential to address the cross-border nature of cybercrimes. Government Legislation: Governments worldwide are enacting legislation to combat cybercrime and hold perpetrators accountable for their actions. As technology continues to evolve, ethical hacking and responsible cybersecurity practices are essential in maintaining a safe and secure digital environment for individuals, businesses, and society as a whole.
Ethical hacking plays a crucial role in improving cybersecurity and fostering innovation, while malicious hacking poses significant risks to privacy, finances, and digital infrastructure. In conclusion, the world of hacking is a complex landscape with both positive and negative implications. Conclusion: The CVV shop menace poses a grave threat to our increasingly digitalized financial landscape. By joining forces, we can create a safer online environment, protect our financial resources, and fortify the foundations of the digital economy against the pernicious influence of CVV shops.
 As online and card-not-present transactions become increasingly common, understanding the role of CVV codes with debit cards is essential for ensuring secure transactions and protecting your financial information. This article provides insights into what CVV codes are, why they are important, and how to use them effectively when making debit card transactions. Compliance: Legitimate businesses that handle payment card data are bound by strict compliance standards, such as the Payment Card Industry Data Security Standard (PCI DSS), to ensure data protection and prevent breaches.
As online and card-not-present transactions become increasingly common, understanding the role of CVV codes with debit cards is essential for ensuring secure transactions and protecting your financial information. This article provides insights into what CVV codes are, why they are important, and how to use them effectively when making debit card transactions. Compliance: Legitimate businesses that handle payment card data are bound by strict compliance standards, such as the Payment Card Industry Data Security Standard (PCI DSS), to ensure data protection and prevent breaches.
 These wallets often employ biometric authentication, adding an extra layer of security. Remember, awareness is a powerful tool in the ongoing battle against deception in the digital world. In the digital age, arming yourself with knowledge is the most potent defense against online scams and fraud. By researching different types of scams, staying informed,
These wallets often employ biometric authentication, adding an extra layer of security. Remember, awareness is a powerful tool in the ongoing battle against deception in the digital world. In the digital age, arming yourself with knowledge is the most potent defense against online scams and fraud. By researching different types of scams, staying informed, 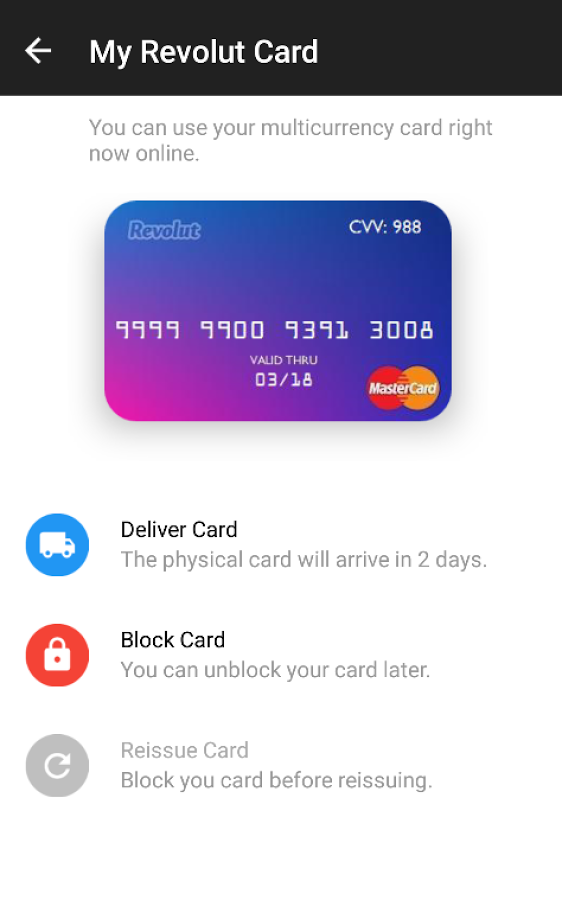 Empowerment through knowledge and proactive actions remains the key to defending against this ever-present threat. They exploit relationships to manipulate victims into providing money or sensitive information. Impersonation: Some scammers impersonate trusted individuals, such as tech support agents, family members, or friends. Staying informed and educating others about these tactics can contribute to a safer online environment for everyone. By understanding their strategies, recognizing red flags, and practicing caution in online interactions, you can significantly reduce your risk of falling victim to their fraudulent schemes.
Empowerment through knowledge and proactive actions remains the key to defending against this ever-present threat. They exploit relationships to manipulate victims into providing money or sensitive information. Impersonation: Some scammers impersonate trusted individuals, such as tech support agents, family members, or friends. Staying informed and educating others about these tactics can contribute to a safer online environment for everyone. By understanding their strategies, recognizing red flags, and practicing caution in online interactions, you can significantly reduce your risk of falling victim to their fraudulent schemes. Mobile Wallets: Mobile wallets have revolutionized the way we make payments by turning smartphones into virtual wallets. These wallets often employ biometric authentication, adding an extra layer of security. Awareness and Education: Consumers need to be aware of the risks associated with cardable sites non VBV and should practice secure online habits, such as using strong passwords and regularly monitoring their accounts.
Mobile Wallets: Mobile wallets have revolutionized the way we make payments by turning smartphones into virtual wallets. These wallets often employ biometric authentication, adding an extra layer of security. Awareness and Education: Consumers need to be aware of the risks associated with cardable sites non VBV and should practice secure online habits, such as using strong passwords and regularly monitoring their accounts. Hacking, in its ethical form known as “white hat” hacking, involves testing systems for vulnerabilities and strengthening security measures. Online platforms allow ethical hackers to share insights, techniques, and experiences, ultimately contributing to improved cybersecurity practices. By understanding the benefits of this method,
Hacking, in its ethical form known as “white hat” hacking, involves testing systems for vulnerabilities and strengthening security measures. Online platforms allow ethical hackers to share insights, techniques, and experiences, ultimately contributing to improved cybersecurity practices. By understanding the benefits of this method,