Understanding the tactics employed by cybercriminals, recognizing the potential risks, and adopting proactive security measures are essential to safeguarding financial transactions. Conclusion: The prevalence of cyber card hacks underscores the critical importance of cybersecurity in today’s digital landscape. By staying informed and practicing vigilant online behavior, individuals and businesses can better defend against cyber card hacks and contribute to a more secure online environment for all.
Card Not Present (CNP) Fraud: CNP fraud occurs when the physical card is not required for a transaction, as in online or phone purchases. Fraudsters use stolen card information to initiate these transactions, often bypassing security measures like the !!!!! Sell DUMPS + CVV !!!!!! code. In conclusion, hackers target bank accounts with credit cards due to the financial gain, potential for identity theft, and demand for stolen data. Recognizing the motives behind these attacks underscores the importance of proactive cybersecurity practices to safeguard sensitive financial information and mitigate the risks associated with cybercrime.
They might also employ tactics like account takeover, where they gain control of an individual’s online account to make fraudulent transactions. Online Shopping Fraud: Fraudsters exploit the convenience of online shopping by using stolen credit card information to make unauthorized purchases. Once they gain access to an individual’s bank account, they can tap into the linked credit card information. Weak Security Practices: Hackers often exploit weak security practices, such as using easily guessable passwords or falling for phishing scams.
Phishing and Social Engineering: Fraudsters often rely on social engineering techniques to manipulate individuals into sharing their credit card details. They send phishing emails or text messages that appear to be from legitimate sources, asking recipients to provide sensitive information such as card numbers, CVV codes, or login credentials. Account Takeovers: Cybercriminals use Mail Pass Fresh to gain unauthorized access to individuals’ online accounts, ranging from social media to email and e-commerce platforms.
Once they infiltrate these accounts, they can exploit personal data for various purposes, including further hacking and financial fraud. Credit card details, personal identification, and financial records are all accessible within these accounts, allowing hackers to exploit this information for their gain.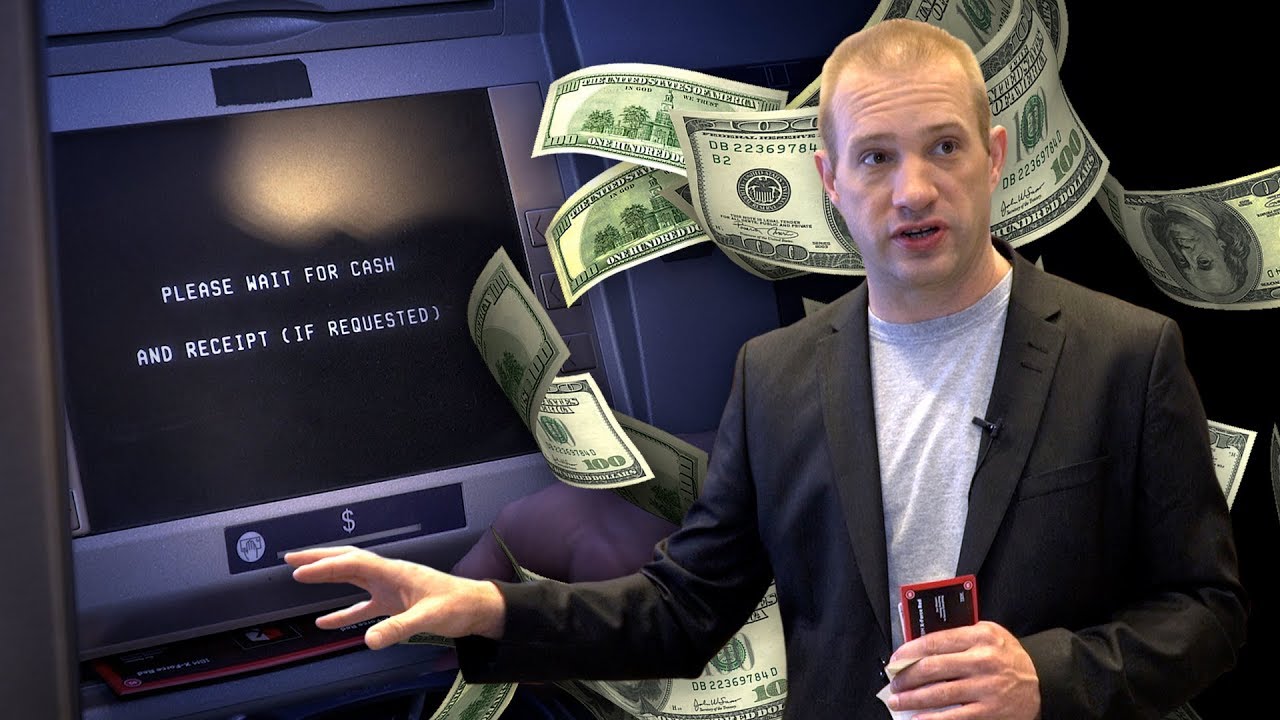
 Conclusion: Buying gift cards without CVV may seem like a shortcut for individuals seeking anonymity, but it’s important to understand the broader implications of this practice. By adhering to legal and ethical online practices, consumers can protect themselves and contribute to a safer digital landscape. It not only undermines security measures but also contributes to the perpetuation of fraudulent activities. Fraudulent Transactions: The data sold in CVV shops is often used for fraudulent activities, including unauthorized purchases, ltd-cc (
Conclusion: Buying gift cards without CVV may seem like a shortcut for individuals seeking anonymity, but it’s important to understand the broader implications of this practice. By adhering to legal and ethical online practices, consumers can protect themselves and contribute to a safer digital landscape. It not only undermines security measures but also contributes to the perpetuation of fraudulent activities. Fraudulent Transactions: The data sold in CVV shops is often used for fraudulent activities, including unauthorized purchases, ltd-cc ( The realm of cybercrime is characterized by its complexity and ever-evolving techniques. Among the concerning activities within this domain is the hacking of card dumps with Track 1&2 data and PIN information. This article delves into the motivations driving hackers to pursue such illicit endeavors and highlights the implications of these actions for individuals and WorldCvv (
The realm of cybercrime is characterized by its complexity and ever-evolving techniques. Among the concerning activities within this domain is the hacking of card dumps with Track 1&2 data and PIN information. This article delves into the motivations driving hackers to pursue such illicit endeavors and highlights the implications of these actions for individuals and WorldCvv (
 The ability to validate CVV information in real-time not only reduces the risk of fraudulent activities but also offers a smoother user experience and benefits businesses by safeguarding transactions. As technology continues to evolve, the adoption of innovative solutions like instant registration holds the potential to revolutionize online payment security, fostering a more secure and efficient digital ecosystem for users and businesses alike. This article aims to shed light on why these activities constitute fraud and the potential implications for victims and the broader cybersecurity ecosystem.
The ability to validate CVV information in real-time not only reduces the risk of fraudulent activities but also offers a smoother user experience and benefits businesses by safeguarding transactions. As technology continues to evolve, the adoption of innovative solutions like instant registration holds the potential to revolutionize online payment security, fostering a more secure and efficient digital ecosystem for users and businesses alike. This article aims to shed light on why these activities constitute fraud and the potential implications for victims and the broader cybersecurity ecosystem.